If you run pop or push traffic, you already know the problem: 30-60% of zones are sending you bots. You're paying real money for fake clicks that will never convert, never engage, never generate a single cent of revenue.
Most bot detection tools run one or two checks — maybe an IP blocklist, maybe a simple User-Agent filter. That's fine for Google Ads PPC where traffic is pre-filtered. But pop and push traffic is raw. It comes from publisher websites with zero quality control. A simple IP check misses headless browsers. A UA filter misses Chrome emulators. A JavaScript challenge misses server-side bots that never load your page.
Single-layer detection catches about 60% of bot traffic on pop campaigns. The other 40% gets through.
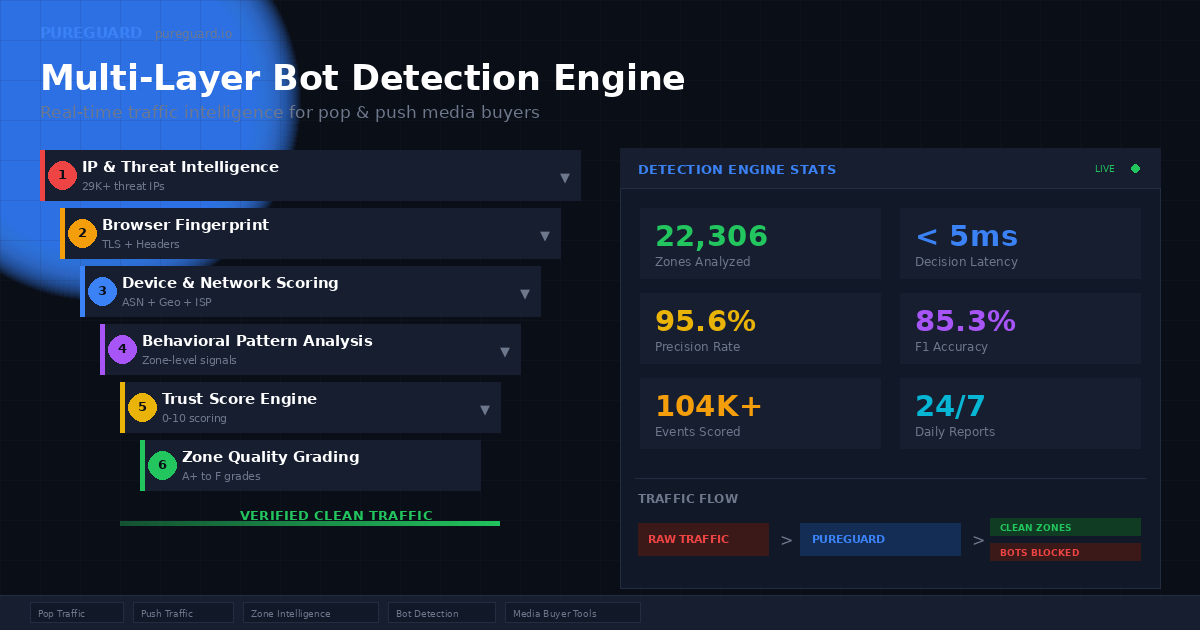
We built something different. Six independent detection layers, each cross-verifying the others, making a decision in under 5 milliseconds. Here's how it works — and why each layer matters for pop and push specifically.
Why Pop & Push Traffic Needs Multi-Layer Detection
Pop traffic (popunder, popup) and push notification traffic share a unique challenge: the traffic source has very little control over who sends the click. When a publisher puts a pop script on their site, anyone who visits triggers it — real humans, bots, scripts, browser extensions, headless farms.
Compare this to search ads, where Google pre-filters traffic before you ever see it, or social ads, where Facebook verifies accounts. Pop networks like PopCash, HilltopAds, RollerAds, and PopAds are selling raw access to publisher inventory. The filtering is your problem.
This means the bots you encounter in pop traffic are fundamentally different from PPC click fraud:
| Bot Type | PPC Click Fraud | Pop/Push Bot Traffic |
|---|---|---|
| Origin | Competitors clicking ads | Bot farms, malware, datacenter scripts |
| Browser | Real browsers (human clicking) | Headless Chrome, emulators, spoofed UAs |
| IP Type | Residential (real competitor) | Datacenter, hosting, VPN, proxy |
| Volume | Dozens per day | Thousands per hour |
| Sophistication | Low (just clicking) | High (fingerprint spoofing, header injection) |
| Detection Method | Click pattern + IP blocking | Multi-layer cross-verification required |
This is why tools built for Google Ads — PPC fraud tools, PPC fraud tools, PPC Protect — don't work on pop traffic. They're solving a completely different problem.
The Multi-Layer Detection Architecture
Our detection engine processes every single click through six independent analysis layers. Each layer examines a different dimension of the request. A click must pass all six to be accepted as human.
The key insight: each layer catches different bots. IP reputation catches known threat sources. Browser fingerprinting catches headless browsers. Network analysis catches datacenter traffic. No single layer is enough — but together, they achieve 95.6% precision with an 85.3% F1 accuracy score.
Layer 1: IP & Threat Intelligence
Every click is checked against continuously updated threat intelligence feeds. We cross-reference multiple community-maintained blocklists covering botnets, scanners, brute-force attackers, and known bad infrastructure. The database currently contains 29,000+ confirmed threat IPs, updated automatically every few hours.
For pop traffic specifically, this layer catches IPs that have been flagged across the entire internet for malicious activity — not just ad fraud, but also port scanning, credential stuffing, and vulnerability probing. If an IP is attacking web servers globally, it's not a real user clicking your pop ad.
Pop/push relevance: Some bot operators reuse their infrastructure across multiple campaigns. An IP that was caught running a click farm on one network often shows up sending traffic through others. This layer ensures known-bad infrastructure is blocked instantly, before any other analysis runs.
Layer 2: Browser Fingerprint Analysis
Real browsers send a specific set of headers that are extremely difficult to fake correctly. Modern Chrome (version 110+) implements the W3C User-Agent Reduction specification, which actually helps detection — we can verify whether a browser claiming to be Chrome 131 is behaving exactly like Chrome 131 should behave.
Our fingerprint analysis checks:
- Sec-Fetch headers — Browser-enforced, unforgeable headers that real browsers send automatically. Missing Sec-Fetch on a desktop Chrome claim? That's a headless browser or a script.
- TLS protocol version — Real Chrome 131 uses TLS 1.3. A request claiming Chrome 131 but connecting via TLS 1.0? Automated tool.
- Header consistency — Real browsers send Accept-Encoding, Sec-CH-UA, and other headers in a consistent pattern. Bots almost always get this wrong.
- Chrome version analysis — We verify that the Chrome build number matches what that version actually ships. Fake versions, impossible build numbers, and deprecated formats are all detected.
Pop/push relevance: This layer is critical for pop traffic because the most common bot technique is running headless Chrome to simulate real browser clicks. These tools send a Chrome User-Agent but miss the subtle header behaviors that real Chrome exhibits. Our engine checks multiple header dimensions simultaneously — getting one right is easy, getting all of them right is nearly impossible for automated tools.
Layer 3: Device & Network Scoring
Real humans browse the internet from residential ISPs — Comcast, AT&T, Deutsche Telekom, True Internet (Thailand), Telkomsel (Indonesia). Bots run from AWS, Google Cloud, DigitalOcean, OVH, Hetzner, and hundreds of smaller hosting providers.
We maintain a database of 50+ datacenter and hosting ASN networks with GeoIP cross-verification. When a click comes from a residential IP, it gets a trust bonus. When it comes from a known hosting provider, it gets a penalty — but crucially, it doesn't get instantly blocked.
Why? Because some legitimate traffic does come through VPNs and corporate proxies. A single datacenter signal isn't enough to block — but when combined with other layer signals (no Sec-Fetch headers + datacenter IP + suspicious Chrome version), the combined evidence is overwhelming.
Pop/push relevance: We've found that datacenter traffic accounts for 15-25% of bot traffic on pop campaigns. These are server-side scripts running from cloud instances, generating thousands of fake clicks per hour. Network analysis catches them before they waste your budget.
Layer 4: Behavioral Pattern Analysis
Sophisticated bots can fake headers and spoof device information. What they can't easily fake is behavior. Real humans don't click 50 times per minute from the same IP. Real humans don't arrive in perfectly timed intervals. Real humans don't generate identical request patterns across different sessions.
Our behavioral engine tracks:
- Burst detection — Multiple clicks from the same IP within a short time window. Real humans might trigger one or two pops per browsing session. Bots generate dozens.
- Timing patterns — Machine-generated traffic often arrives in suspiciously regular intervals. Human traffic is naturally irregular.
- Cross-session correlation — When the same IP, ASN, or device fingerprint appears across multiple zones with identical patterns, it indicates coordinated automation.
Pop/push relevance: Pop traffic is particularly vulnerable to burst attacks where a bot operator generates hundreds of clicks in minutes to inflate zone statistics. Our burst detection uses in-memory rate limiting that responds in microseconds — fast enough to catch bursts before they accumulate meaningful spend.
Layer 5: Trust Score Engine
This is where the magic happens. Instead of a binary "bot or not" decision, every click receives a continuous trust score from 0 to 10 based on all evidence from the previous four layers.
The scoring isn't a simple sum — it's a weighted model where certain combinations of signals are far more damning than individual signals alone:
A residential IP with valid Sec-Fetch headers, correct Chrome build, and proper TLS version might score 7.5 — clearly human. The same Chrome version from a datacenter IP with missing Sec-Fetch and no Accept-Encoding? Trust score 1.2 — confirmed bot.
The threshold is configurable per campaign. Most media buyers set it at 5.5, which provides the optimal balance between catching bots and preserving real traffic. Our data across 22,000+ zones shows this threshold achieves:
- 95.6% precision — When we say it's a bot, it's a bot 95.6% of the time
- 85.3% F1 accuracy — The harmonic mean of precision and recall, measuring overall detection quality
- Under 5ms decision time — Fast enough for real-time pop traffic without adding latency
Pop/push relevance: Trust scoring is essential for pop traffic because the line between "human" and "bot" isn't always clear. A single suspicious signal shouldn't block a real person. But three suspicious signals together? That's a bot. The trust score captures these nuances in a way that simple rule-based systems cannot.
Layer 6: Zone Quality Intelligence
This is the layer that turns bot detection into zone intelligence — the ability to know which publisher zones are worth buying and which are burning your budget.
Every zone that sends traffic through PureGuard gets continuously graded based on aggregate performance:
| Grade | Accept Rate | What It Means |
|---|---|---|
| A+ | 95%+ human | Gold zone. Scale spend here. |
| A | 80-95% human | Strong zone. Maintain spend. |
| B | 70-80% human | Decent zone. Monitor for changes. |
| C | 50-70% human | Mixed quality. Watch closely. |
| D | 30-50% human | Poor quality. Consider blocking. |
| F | Below 30% | Bot zone. Blocked automatically. |
But the grading goes deeper than just accept rate. Our zone intelligence engine examines pattern signals across the entire zone's traffic history:
- Hosting IP concentration — What percentage of the zone's traffic comes from datacenter IPs? Above 30%? That's a hosting botnet, not a real publisher.
- WebView rate — Is the zone generating an unusual amount of Android WebView traffic? High WebView + hosting IPs = classic bot farm signature.
- Device authenticity — Real device signals (actual screen dimensions, genuine Chrome builds, proper Client Hints) vs. generic or spoofed device data.
- Trust score distribution — A healthy zone has most clicks scoring 6-9. A bot zone clusters around 2-4 with a few high-trust outliers.
The system grades over 22,000 zones and growing. Every media buyer using PureGuard gets daily zone intelligence reports delivered to their inbox — showing which zones to block, which to watch, and which to scale.
Pop/push relevance: This is the game-changer for media buyers. Instead of manually checking zone performance in your tracker, you get an automated grading system that tells you exactly where your money is going. Block the F-grade zones, scale the A+ zones, and watch your ROI improve immediately.
Real Performance Data
Here's what the multi-layer system looks like in production, across real pop and push campaigns:
The median decision time is 4.4 milliseconds. That's faster than a single DNS lookup. Your pop redirect happens with zero perceptible delay — the user never knows they were verified.
How Each Layer Catches What Others Miss
The real power isn't any single layer — it's the cross-verification between them. Here's a real example from our production data:
- Layer 1 (IP): Clean — not on any blocklist PASS
- Layer 2 (Fingerprint): Chrome 131 UA, but missing Sec-Fetch-Dest header FLAG
- Layer 3 (Network): IP belongs to Hetzner hosting FLAG
- Layer 4 (Behavior): 12 clicks in 90 seconds from same IP FLAG
- Layer 5 (Trust): Combined score = 1.8/10 BLOCK
- Layer 6 (Zone): Zone already graded F from historical pattern BLOCKED
A single-layer IP check would have let this through. The multi-layer approach caught it with 3 independent signals.
And the reverse — making sure we don't block real humans:
- Layer 1 (IP): Clean — residential ISP PASS
- Layer 2 (Fingerprint): Chrome 131, all Sec-Fetch headers present and valid PASS
- Layer 3 (Network): Deutsche Telekom residential PASS
- Layer 4 (Behavior): Single click, no burst pattern PASS
- Layer 5 (Trust): Combined score = 7.8/10 ACCEPT
- Layer 6 (Zone): Zone graded B, healthy traffic mix ACCEPTED
Six layers all agree: this is a real human. Accept with high confidence.
What This Means for Your Campaigns
If you're running pop or push traffic at scale, here's what multi-layer detection does for your bottom line:
1. Stop Paying for Bot Clicks
Our data shows the average pop campaign wastes 30-40% of budget on bot traffic. At $1,000/day spend, that's $300-400/day going to bots. Per month, you're burning $9,000-12,000 on traffic that will never convert. Multi-layer detection blocks these before they consume your budget.
2. Find the Gold Zones
Out of 22,000+ zones we've analyzed, only 0.2% earn A+ (gold) status. These are the zones where 95%+ of traffic is verified human. Most media buyers never find them because they're buried under thousands of mediocre and bot-infested zones. Zone intelligence surfaces them automatically.
3. Get Daily Actionable Intelligence
Every morning, PureGuard sends you a zone intelligence report grading every zone that received traffic yesterday. F-grade zones come with a copy-paste blocklist. A+ zones are highlighted for scaling. No manual analysis required.
4. Prove It Before Committing
Shadow mode lets you run detection on your live traffic without blocking anything. You see exactly how much of your budget goes to bots — with full evidence for every blocked click. When you're ready, flip the switch and start saving.
Built for Pop & Push — Not Adapted From PPC
Most bot detection tools were built for Google Ads and adapted (poorly) for other traffic types. PureGuard was built from day one for pop, push, and native traffic. Every detection rule, every scoring threshold, every zone intelligence algorithm was calibrated on real pop and push campaign data.
This matters because:
- Pop traffic has no click intent — Users don't choose to see a pop. Bot detection must work without behavioral pre-signals that PPC tools rely on.
- Push traffic has notification-level engagement — Click patterns on push are fundamentally different from search ads. Our behavioral models are calibrated for this.
- Zone-level intelligence matters — PPC tools block IPs. Pop media buyers need to block zones — entire publisher placements that consistently send bot traffic.
- Speed is non-negotiable — Pop redirects happen in real-time. Adding 100ms of detection latency costs you money. Our 4.4ms median decision time adds zero perceptible delay.
- Price is proportional — Enterprise bot detection costs $3,000-50,000/month. Pop media buyers work on thin margins. PureGuard is built for the economics of arbitrage and direct-response campaigns.
Networks We Support
PureGuard works with any pop or push traffic source. Pre-built integrations with automatic zone tracking and macro support for:
Setup takes under 5 minutes. Add your campaign URL to a connector, paste the PureGuard link as your destination URL in the ad network, and detection starts immediately. No JavaScript tags to install, no SDK to integrate, no DNS changes required.
Try It On Your Traffic — Free
If you're spending more than $50/day on pop or push traffic, you're almost certainly losing money to bots. The question is how much.
PureGuard's free tier gives you 100,000 checks — enough to audit your current campaigns and see exactly where your budget is going. Full trust score breakdown on every click, zone quality grades, and daily intelligence reports included.
See Multi-Layer Detection on Your Traffic
Connect your pop or push campaign and get real-time zone intelligence. See which zones are sending you bots and which ones are gold.
Start Free Detection100K checks free. Daily zone intelligence reports. No credit card required.